Authenticator Apps aren’t Passwordless. It’s SMS with Extra Steps.
Analysis into the security of phone numbers in the cybersecurity stack
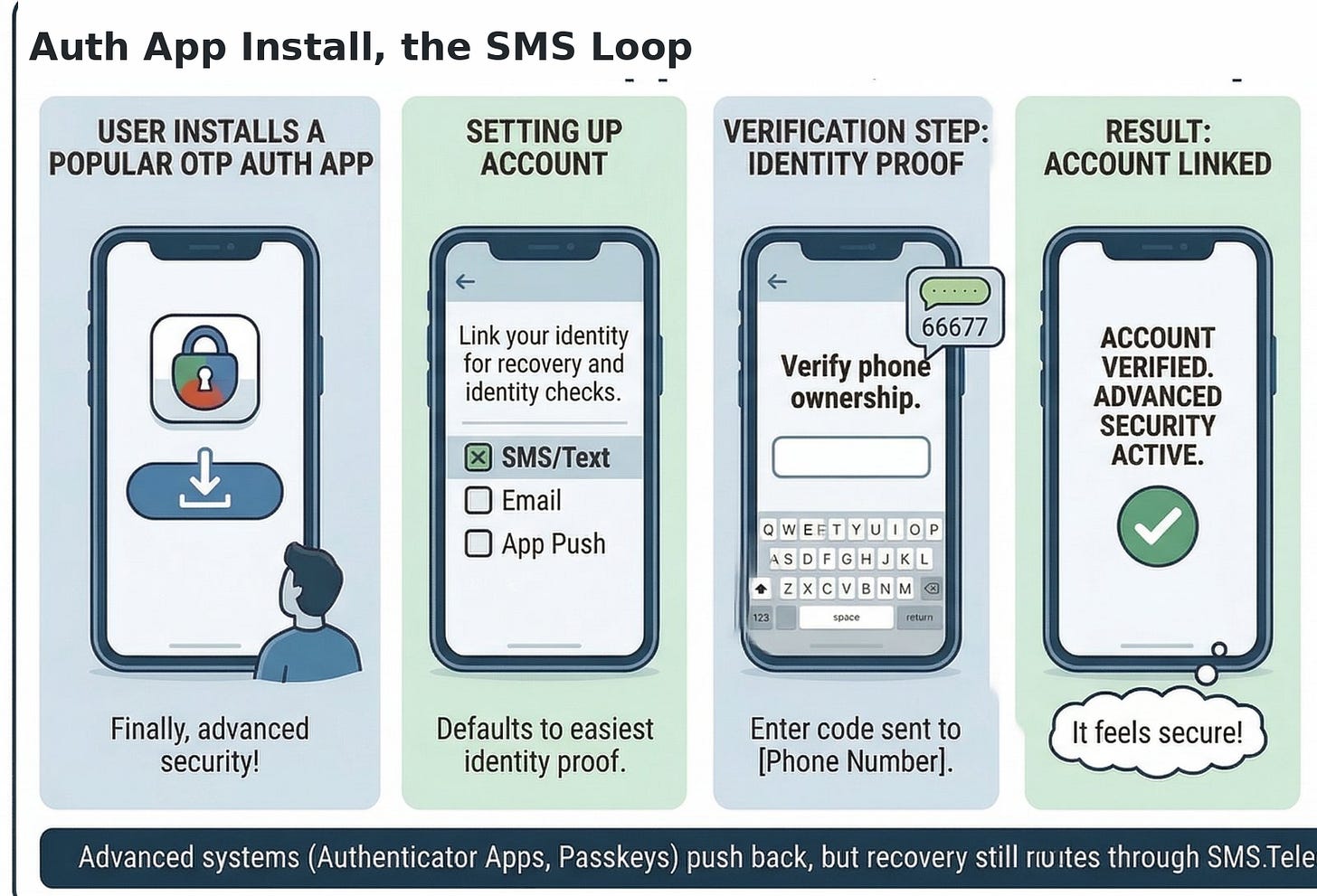
You break your phone. You buy a new one. You download Microsoft Authenticator because you’re a responsible adult who listened to the security community. You open the app. It asks you to verify your identity.
How? SMS. A six-digit code texted to your phone number.
The thing that was supposed to replace SMS-based authentication can’t bootstrap itself without SMS-based authentication. That’s not a bug in the implementation. That’s the architecture telling you something the security consensus doesn’t want to hear.
What’s Already Happened
In January 2024, a 25-year-old from Alabama walked into an AT&T store in Huntsville with a fake ID, convinced the clerk to port a phone number to a new SIM card, and used the hijacked number to take over the SEC’s official X account. His co-conspirators posted a fake announcement that the SEC had approved spot Bitcoin ETFs. Bitcoin spiked $1,000 in minutes, then cratered $2,000 when the SEC clarified the breach fifteen minutes later. Eric Council Jr. pleaded guilty and got 14 months.
In March 2025, a California arbitrator ordered T-Mobile to pay $33 million after a SIM swap drained approximately $38 million in cryptocurrency from a single customer’s wallet. This despite the customer having T-Mobile’s “NOPORT” security flag and “extra security” enabled. The attackers convinced a call center agent to issue a remote eSIM QR code, bypassing every safeguard T-Mobile offered. Largest known SIM swap arbitration award in history.
It’s getting worse.Cifas reported a 1,055% surge in UK SIM swaps in 2024. The FBI’s IC3 tracked $26 million in US losses from SIM swaps alone.
These aren’t edge cases. The SEC. A $33 million judgment. A major UK retailer. Phone numbers are treated as identity, and there’s nothing underneath them verifying that the person claiming to own that number actually does.
The security community’s response? Stop using SMS for authentication. Use authenticator apps instead.
Which brings us back to that broken phone.
The Consensus View (And Why It’s Technically Correct)
The FBI and CISA want you to kill SMS-based 2FA. After Chinese hackers breached US telecommunications companies under the codename Salt Typhoon, federal law enforcement issued what the press called an “unambiguous advisory”: stop using SMS codes for authentication.
SMS has no encryption layer, no mutual authentication, no resistance to protocol-level attacks. SS7, the signaling protocol that routes SMS across global carrier networks, was developed starting in the mid-1970s and formalized by the CCITT in 1980, with zero assumption of adversarial access. By 2014, researchers had published proof-of-concept code showing anyone with signaling-layer access could redirect SMS messages. In 2024, attackers exploited SS7 to intercept SMS from thousands of European banking customers.Positive Technologies tested 28 telecom networks and found 100% vulnerable to denial of service.
NIST classified SMS OTP as “RESTRICTED” in 2017. The only authenticator to get that label. But here’s the nuance the coverage missed: NIST did not deprecate SMS OTP. Restricted means organizations must assess risks, offer at least one non-restricted alternative, and maintain a migration plan. NIST explicitly considered a full ban and concluded it couldn’t implement one due to impracticality across federal agencies. The December 2024 FBI/CISA advisory? Its own text states it “specifically addresses highly targeted individuals who are in senior government or senior political positions.” The recommended alternative is FIDO authentication (which includes passkeys, not just physical hardware keys). Authenticator apps are acknowledged as “better than SMS” but “still vulnerable to phishing.”
The FBI wasn’t telling your bank to stop texting account alerts. It was telling cabinet members to use FIDO, whether that’s a hardware key or a passkey on their phone.
The Bootstrap Paradox
Authenticator apps push the security problem forward in time. The vulnerability just moves.
Apple’s iCloud Keychain, the most technically sophisticated recovery mechanism in consumer tech, terminates at SMS in its default recovery path. Apple has offered a Recovery Key since 2013 and Recovery Contacts since 2021 as alternatives. But the default path, the one most consumers actually follow, still routes through a text message.
Microsoft’s Authenticator recovery requires phone or email verification. The FIDO2/WebAuthn spec contains no account recovery mechanism. It’s explicitly punted to relying parties. Google Password Manager recovery falls back to an email or phone number. Chase, Wells Fargo, Bank of America: all offer passkeys, all maintain SMS OTP as fallback.
The structural dependency is circular: Passwordless systems need account recovery. Account recovery needs identity proof. The most universal identity proof is a phone number, verified by SMS — the same SMS that’s vulnerable. The security ceiling of the whole passwordless ecosystem is set by telecom infrastructure.
The passwordless movement is real and correct. The problem is that the transition period has a well-documented weak point: a phone number sitting at the top of the security stack with no intelligence layer underneath it.
The Actual Vulnerability Is a Missing Intelligence Layer
SIM swaps work because carriers have no real-time signal that your number should stay put. SS7 attacks work because the protocol has no authentication layer. The phone number is used as identity, but the identity layer has no security underneath it.
Go back to the SEC hack. The attacker walked into an AT&T store and ported a number. If the relying party (X, in this case) had queried a SIM Swap detection API before accepting the password reset, it would have seen the SIM change in real time and blocked the reset. The entire breach collapses.
The solution isn’t to kill SMS. It’s to build intelligence underneath the phone number.
In November 2025, Vonage launched SIM Swap detection across all three major US carriers: Verizon, AT&T, T-Mobile. The API tells you, in real time, whether the SIM associated with a phone number has been swapped recently. Vonage’s published efficacy: 30–40% improvement in fraud detection. TCompetitors are reporting similar numbers.Twilio reports SIM swap detection reduced SIM-swap-based banking fraud “to nearly zero overnight” in one deployment. Telesign documented preventing approximately 200 SIM swap fraud cases and an estimated $2 million in losses for a single online lending client. When three competitors independently report dramatic efficacy from the same class of API, the directional signal is hard to dismiss.
The logic is structural: if you can see a SIM swap in real time, you can block the downstream fraud. It works. The question is deployment speed.Every SIM swap attack in the Body Count section above is detectable with this single API call. and this is detectable with a single API call — not as a theoretical exercise, but in production.
Silent Authentication, also launched by Vonage across US carriers in November 2025, is the more radical play. It doesn’t require an OTP at all. It uses the mobile data connection from an active SIM to verify that the device making a request currently has that SIM. There’s no code to intercept and no endpoint visible to SS7 attackers. The verification happens at the network layer. The user never sees it, and there’s nothing for an attacker to redirect.
The constraint worth naming: Silent Authentication requires an active cellular data connection. Wi-Fi only or VPN? The base product can’t verify. An advanced version built on GSMA TS.43 handles those scenarios but is still in alpha.
Vonage’s early deployments report 3–5x faster authentication and an 8 percentage point lift in conversion rates versus traditional SMS OTP. Again, other vendors see the same pattern:IPification reported a 58% improvement in mobile registration conversion rates for Tiger Brokers after integrating network-based silent authentication. Prove (formerly Payfone) documented 79% faster customer onboarding and a 15% increase in sign-ups via an AWS case study. Vonage’s 8-point lift actually looks conservative next to those numbers. All vendor-reported, but the pattern across independent implementations is consistent enough to act on.
If SIM Swap detection is the defensive play (catch the fraud before it lands), Silent Authentication is the offensive one. It removes the attack surface entirely by eliminating the OTP from the flow.
These aren’t replacements for SMS OTP. They’re infrastructure that sits underneath SMS, authenticator apps, passkeys, and passwordless systems. They secure the phone-number-as-identity layer that every one of these approaches still touches.
Five Layers That Change Everything
Here’s the architecture. I work at Vonage, so I’ll use our API names — but this maps equally to Twilio, Sinch, and Telesign. I’ve walked enough security teams through this stack to know which layer gets the most pushback. It’s always Layer 4, because the first question every CISO asks is: what happens when they’re on Wi-Fi?
Layer 1 — Phone Number Validity. Filter out burners, dead numbers, known fraud numbers.
Layer 2 — Risk Scoring. VoIP? Recently ported? Fraud network history? Risk scoring catches this before you send any code.
Layer 3 — SIM Swap Recency. Has the SIM been swapped recently? SIM Swap detection APIs query carrier infrastructure in real time to check if the SIM attached to this number has changed ownership within a defined window (typically the last 30 days). The API returns a risk score and a timestamp. If there’s been a swap, it happened during the attack window, and you block. If there hasn’t, you proceed. -This is the layer that stops every attack in the Body Count.
Layer 4 — Active Device Binding. Does the device currently have this SIM? Silent Authentication verifies at the network layer—no OTP, no code, nothing for an attacker to intercept. -This is the layer that makes the OTP optional.
Layer 5 — OTP Delivery. Only after the phone number has passed layers 1–4 do you send the OTP. By this point, the SIM hasn’t been swapped. The number is real and low-risk. The device matches.
This stack doesn’t kill SMS OTP. It makes SMS OTP actually secure. And it simultaneously makes authenticator app recovery flows secure, passkey device binding secure, and passwordless bootstrap flows secure. Every one of those systems still uses a phone number somewhere.
Where This Leaves SMS
The security community isn’t wrong to push passwordless. Passkeys, device-bound FIDO2 credentials on your phone’s secure enclave, are the most realistic near-term successor to SMS OTP for consumer auth. But passkeys don’t eliminate the phone number from the identity stack — they just move it. Every synced passkey system still falls back to account recovery, and account recovery still routes through a phone number. The bootstrap paradox doesn’t disappear with passkeys. It gets buried one layer deeper.
The regulatory pressure is real. Singapore, Malaysia, UAE, India, and the Philippines are all phasing out SMS OTP from banking. But note what they’re actually eliminating: SMS as a user-facing authentication experience. None of them eliminate phone-number-based verification from KYC, account recovery, or device binding. They’re moving the phone number from the top of the security stack to the bottom. That’s not the same as removing it.
SMS OTP will survive. The question is whether the phone number sits naked at the top of the security stack, or at the bottom, encapsulated beneath carrier-level verification that makes SIM swaps detectable and SS7 attacks moot.Juniper Research projects network API revenue will grow from $284 million to $8.1 billion by 2030, with auth and fraud APIs driving 60%+ of that growth.
The smart money is building network intelligence underneath the phone number until it actually deserves the trust we’ve been placing in it.
By the time the market figures out what’s happening, the infrastructure will already be there.
#CPaaS #Cybersecurity #Authentication #FraudPrevention #Telecom